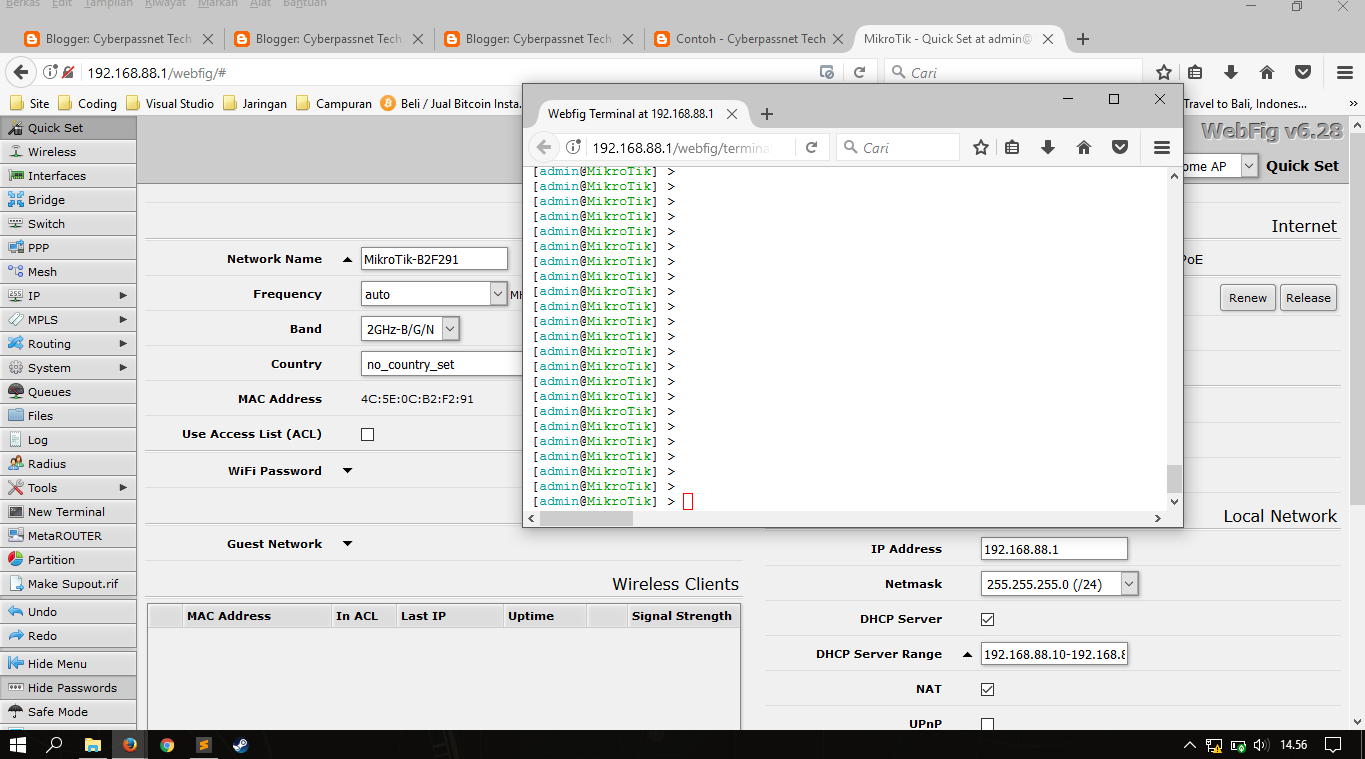
Mikrotik Manual Configuration
It defintily is not. However, the basic configuration is set to fit the needs of most users. Still, some hardening steps must be taken to increase the security of your Mikrotik server by following the below steps. NMAP: Port and Service scanning

Static IP Configuration on Mikrotik ( Terminal)
When connecting the first time to the router with the default username admin and no password ( for some models, check user password on the sticker), you will be asked to reset or keep the default configuration (even if the default config has only an IP address).
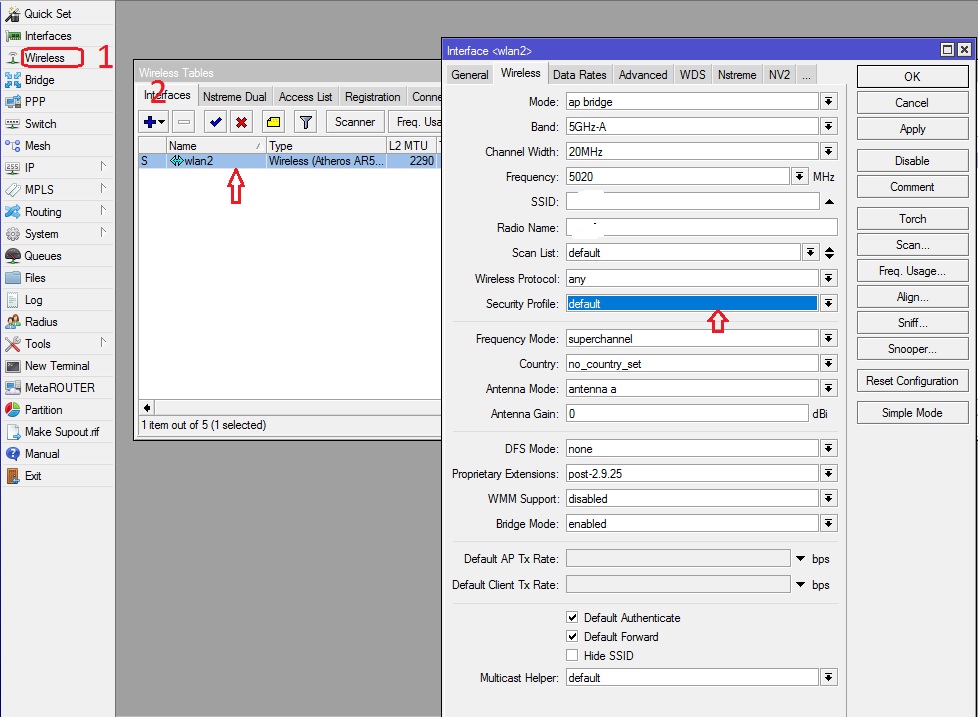
How to create a security profile in Mikrotik Timigate
To show default configuration on your router : /system default-configuration print And if you need to export it : /system default-configuration print file=defconf.txt. MikroTik Security : Built-in Default Configuration "Learn like Newbie, work like Pro" - LucuBRB
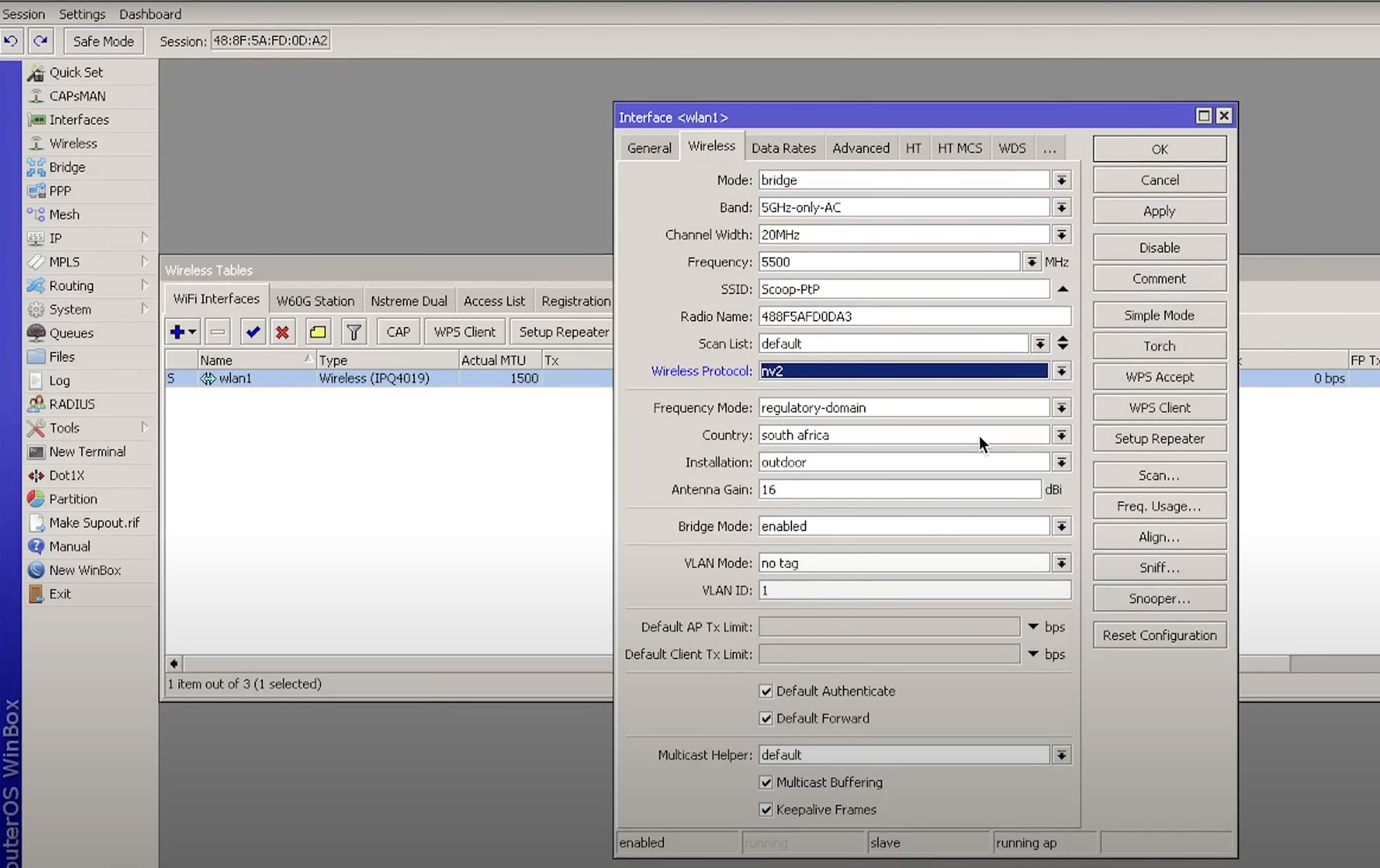
How to Create a MikroTik PtP Bridge Link Scoop
Step-by-step guide. Change default user name: Go to System>Users; Click on + to add a new user ; Insert name and set access rights in Group: full; Type in your secure password; Click OK and enable user; Disable default user: admin. Close the Winbox and login with your new username.
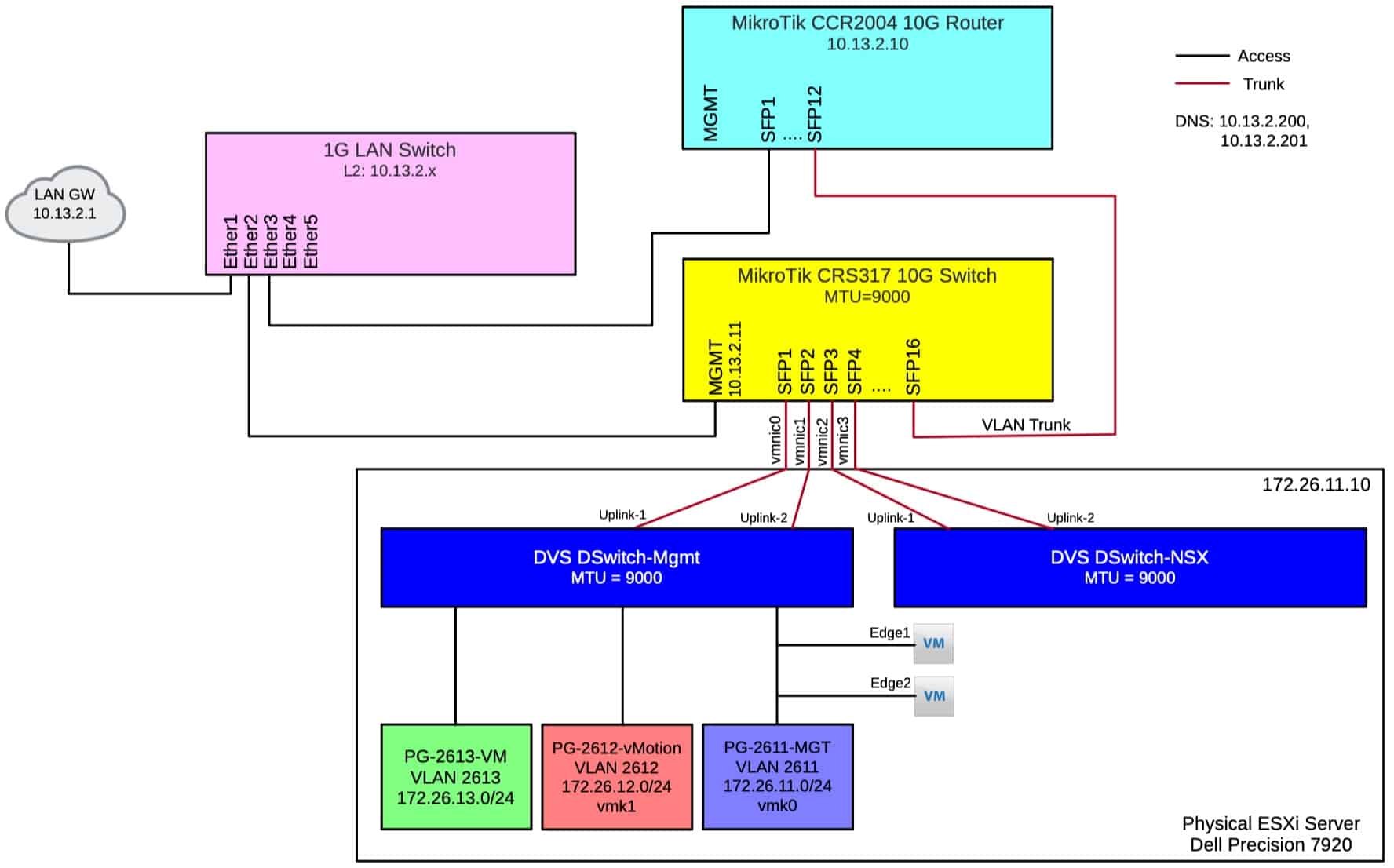
Home Lab MikroTik CCR2004 and CRS317 Configuration Derek Seaman's
I. Configure security mode. Mikrotik wireless router allows to create separate types of security profiles, which will be imposed in the wireless card configuration section. Go to Wireless -> Security Profiles click Add New. Configuring security profiles has many configuration options depending on the intended use, the following information can.

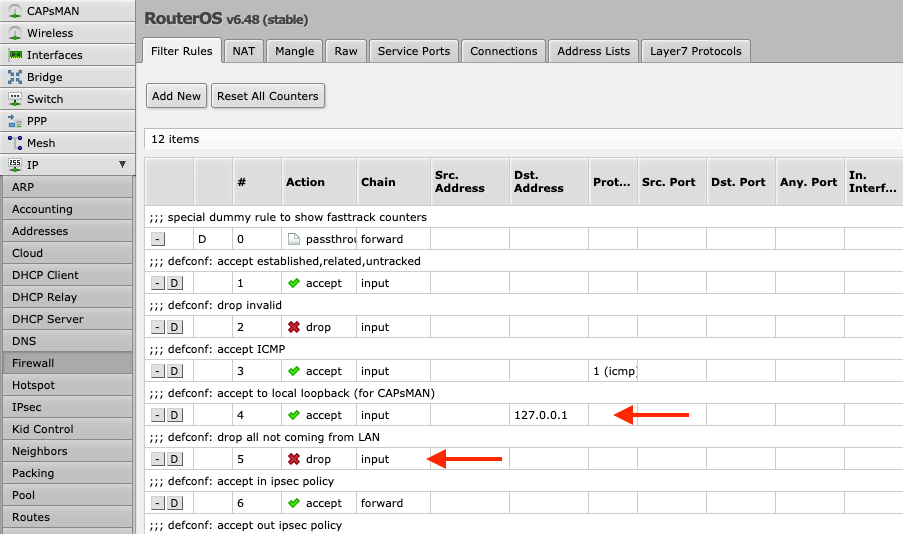
Mikrotik firewall filter rules MikroTik security configuration YouTube
1 Summary 2 Connecting wires 3 Configuring router 3.1 Logging into the router 3.2 Router user accounts 3.3 Configure access to internet 3.3.1 DHCP Client 3.3.2 Static IP Address 3.3.3 Configuring network address translation (NAT) 3.3.4 Default gateway 3.3.5 Domain name resolution 3.3.6 SNTP Client 3.4 Setting up Wireless
Mikrotik CAPsMAN is Awesome (Home Automation) — Kaspars Dambis
#Mikrotik Configuration#Security Guideline. #Mikrotik #protection. Guideline for Mikrotik Configuration. Step0 [0 means do it immediately] /system package update check-for-updates /system routerboard upgrade. Step1(set complex password with special character and disable default admin user).
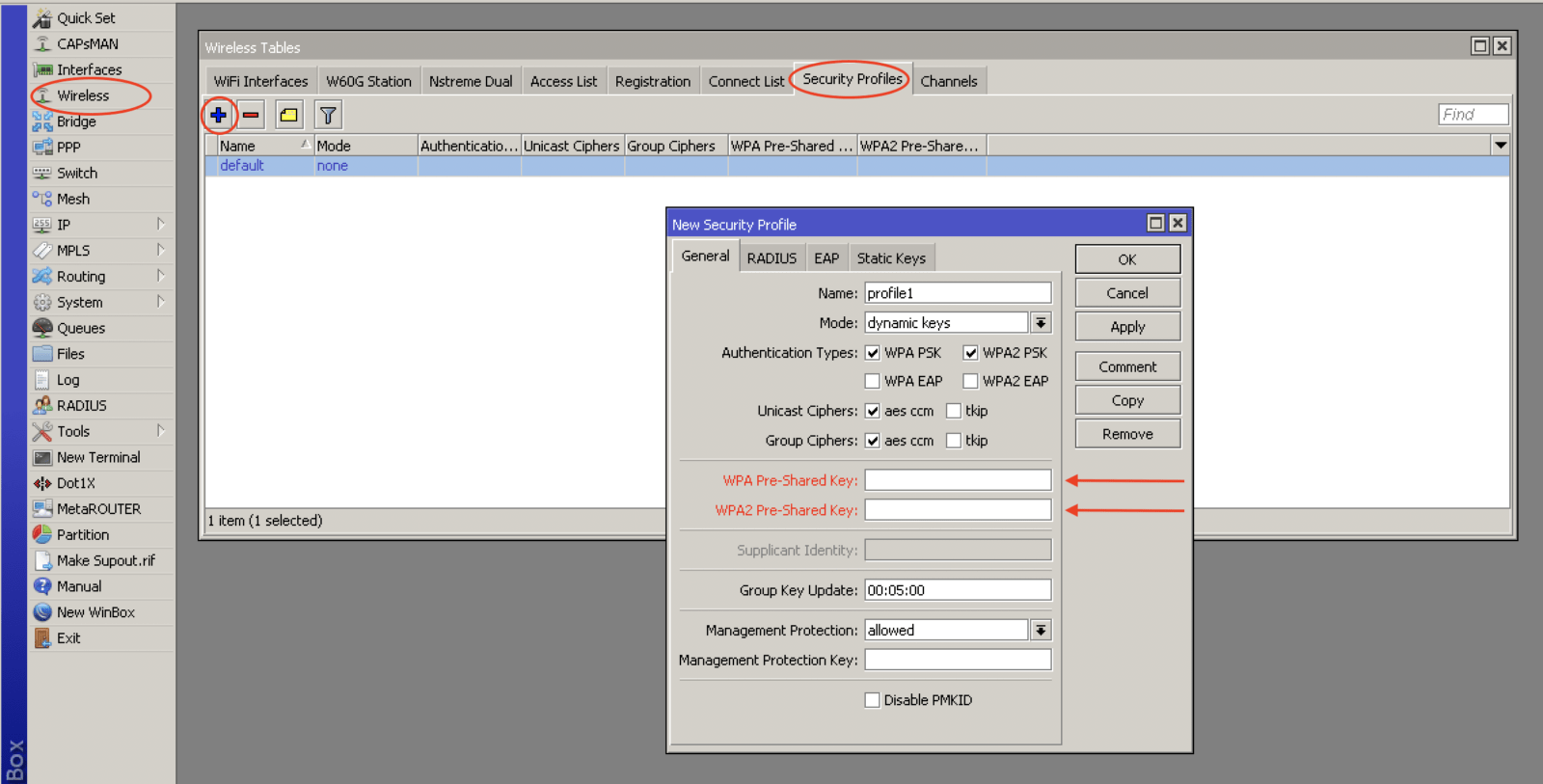
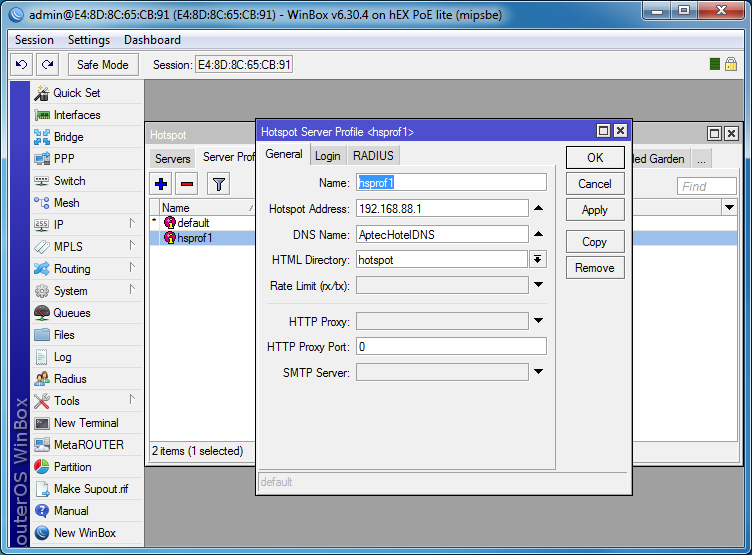
Mikrotik_security_profile Global Hotspot
IP -> Firewall -> Filter. Lets get down to the nitty gritty, firewall filtering. There are 3 chain options: Input - The input chain is traffic destined TO the router. This would be someone trying to ping the router or IPSec traffic destined for the router. Output - The output chain is traffic sourced from the router heading OUT.

Configure and manage your mikrotik security best practice by Anu_diu
Securing RouterOS router. EASY GUIDELINE TO PROTECT YOUR MIKROTIK ROUTEROS ROUTER. Anuwat Ngowchieng. อนุวัตร โง้วเชียง. Consulting Engineer. Internet Thailand Public Company Limited (INET) [email protected]. Certificate: MikroTik: MCTNA, MTCWE Microsoft: MCP, MCSA, MCSE. VMWare: VCP5-DCV.

MikroTik Wireless Security configuration MikroTik Tips & Tricks
#Mikrotik Firewall #Access Restrictions#How to Secure Your Device from Hacker#Winbox port change#Security of input,output,forward rules Setup With MikroTik#P.
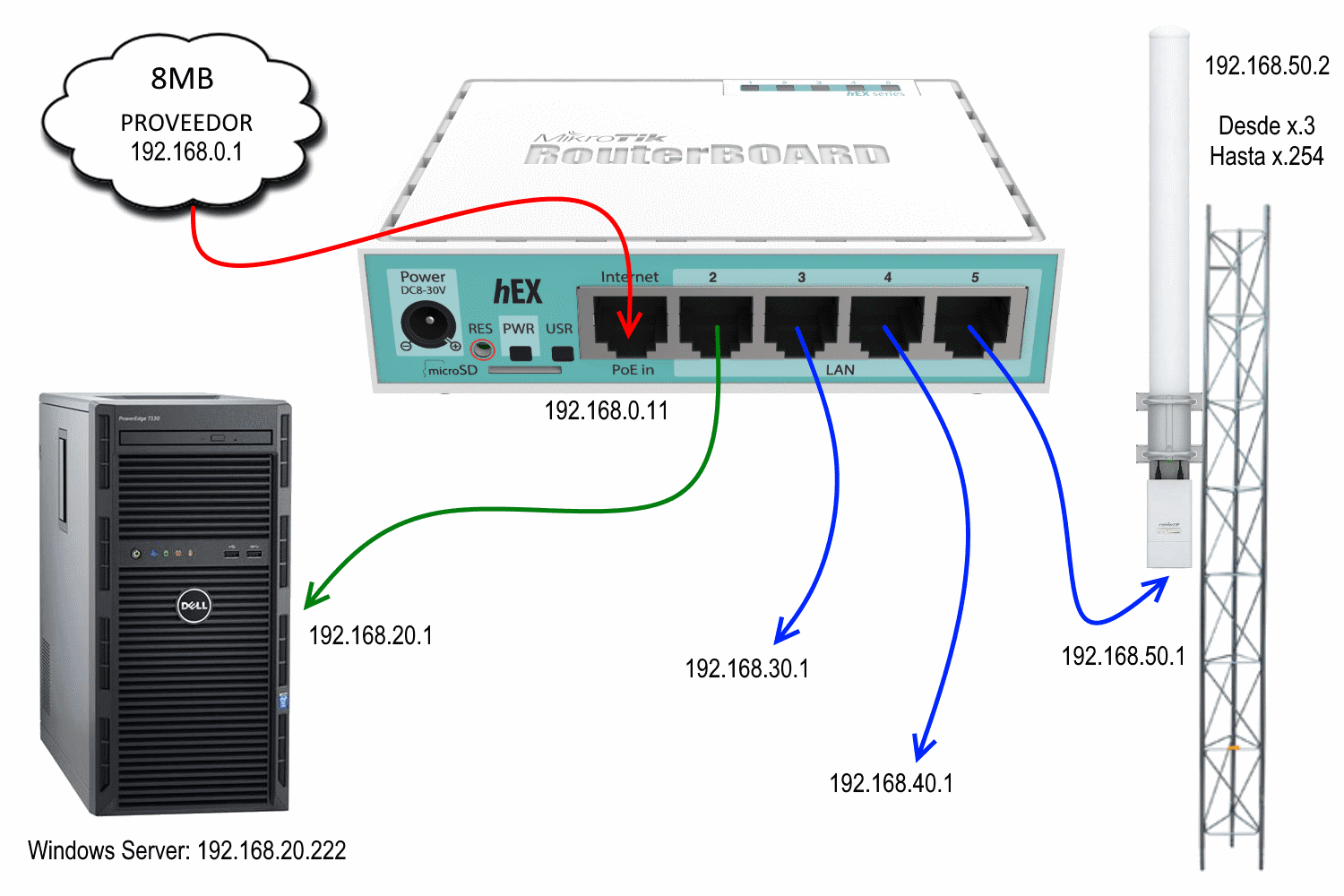
Mikrotik routeros configuration fadtee
Build real networks while studying for Network+. Hardening steps for securing your MikroTik RouterOS devices. Includes user management, firewalls, IP services, and more.

How To Configure Mikrotik Router Start Here Riset
Security is big concern for any network device now. In this video you will learn how to secure your mikrotik router in 6 steps. It is very important to secur.
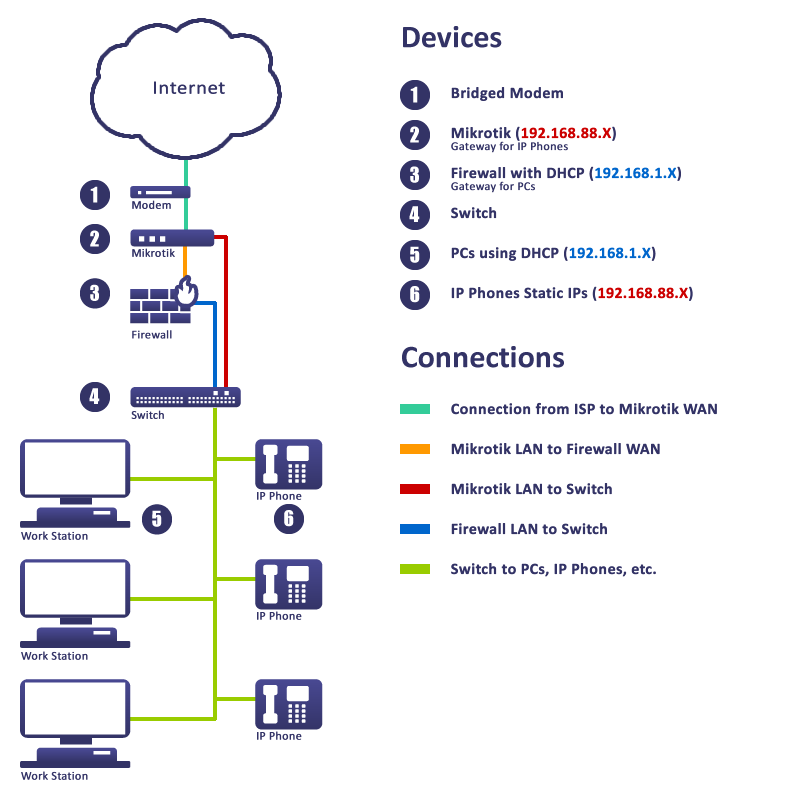
Mikrotik Network Layout using Mikrotik & Firewall Powered by Kayako
3 Router services 3.1 RouterOS services 3.2 RouterOS MAC-access 3.2.1 MAC-Telnet 3.2.2 MAC-Winbox 3.2.3 MAC-Ping 3.3 Neighbor Discovery 3.4 Bandwidth server 3.5 DNS cache 3.6 Other clients services 3.7 More Secure SSH access 4 Router interface 4.1 Ethernet/SFP interfaces 4.2 LCD 5 Firewall 5.1 IPv4 firewall to a router 5.2 IPv4 firewall for clients

How to configure mikrotik from zero config Tutorial YouTube
Security is big concern for any network device now. In this video you will learn how to secure your mikrotik router in 7 steps. It is very important to secur.
How to Configure Mikrotik Using CLI Line Interface
Re: CAPsMAN on v7.13 configuration. When using VLAN's, you can't use datapath (yet) on AC devices. Hopefully this will be resolved in newer versions of RouterOS, up till then you can use this "hack": The "hack" is using VLAN filtering (manually) on the CAP.
Mikrotik2BRouters2BSite2Bto2BSite2BGRE2Bover2BIPSec2BVPN
Overview This article describes a set of commands used for configuration management. Configuration Undo and Redo Any action done in GUI or any command executed from the CLI is recorded in /system history . You can undo or redo any action by running undo or redo commands from the CLI or by clicking on Undo, and Redo buttons from the GUI.